Introduction to Ethical Hacking
Free Ethical Hacking Course for Beginners
This free introduction to ethical hacking course for beginners will teach you the fundamentals of ethical hacking. The course aims to make you aware of ethical hacking threats, the process, and a range of domains where it is used.
What you learn in Introduction to Ethical Hacking ?
About this Free Certificate Course
This ethical hacking course is designed to guide you through the ethical hacking process, complemented by hands-on demonstrations to solidify your understanding. It encompasses a broad range of domains such as Web Application, Mobile Application, and Network Application security. Key subjects covered include common vulnerabilities, ethical hacking strategies, Android-based attacks, and various network attack methodologies. A significant focus is placed on Web Application security, with practical exercises on bWAPP to illuminate its architecture, functionalities, and importance. Through the use of Kali Linux, this free ethical hacking course online immerses participants in real-world challenges such as broken authentication mechanisms, blind SQL injections, and cross-site scripting vulnerabilities. This hacking course provides learners with the critical skills and knowledge needed to learn ethical hacking effectively across different domains, laying a solid foundation for implementing secure and responsible cybersecurity measures.
This Ethical Hacking free course offers an overview of hacking ethics and techniques. It delves into the fundamentals of hacking, computer security threats, and the objectives of ethical hackers. Participants gain insights into the necessary skills and tools for ethical hacking. To take your learning journey to the next level, check out the Postgraduate Program in Cyber Security.
Course Outline
This module covers a fundamental concept – hacking. You will understand what hacking is and its three types: black hat, white hat, and grey hat hackers. Lastly, you will also get familiar with ethical and unethical hacking.
Hacking occurs because of computer security threats such as computer viruses, computer worms, scareware, keylogger, adware, malware, backdoor, trojan, ransomware, and spyware.
In this module, you will learn the goals of ethical hacking. You will understand how ethical hacking is legal and adapted by many organizations.
The learner will learn about various skills to be pursued by ethical hackers. The learners will also get to know about tools used by ethical hackers.
This module covers the ethical hacking process, such as information gathering, scanning, gaining and maintaining access, clearing tracks, and reporting.
Ratings & Reviews of this Course
With this course, you get
Free lifetime access
Learn anytime, anywhere
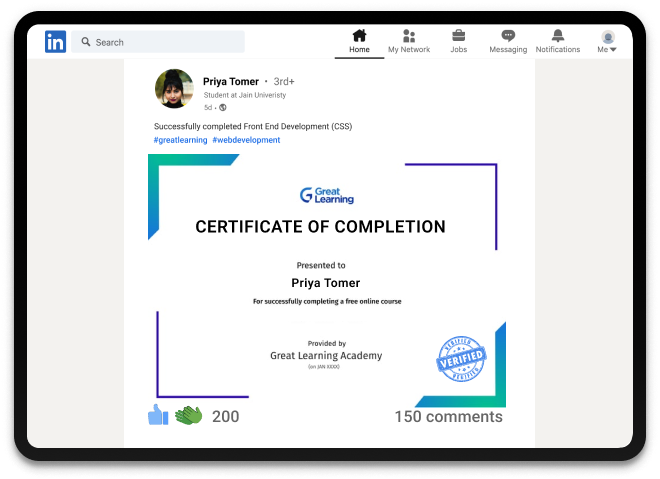
Completion Certificate
Stand out to your professional network
3.0 Hours
of self-paced video lectures
Frequently Asked Questions
What is ethical hacking and how does it differ from illegal hacking?
Ethical hacking involves legally breaking into systems to identify potential threats and vulnerabilities, with the intent of improving security. Unlike illegal hacking, it's done with permission and aims to prevent cyber attacks.
What skills are required to become an ethical hacker?
Essential skills include understanding of networks, operating systems, and programming languages (like Python, JavaScript). Knowledge in cybersecurity practices and tools is also important.
What are the legal and ethical boundaries in ethical hacking?
Ethical hackers must always have explicit permission to access and test systems. They should adhere to legal guidelines and respect data privacy and integrity.
What are common ethical hacking techniques?
Techniques include penetration testing, vulnerability scanning, phishing simulations, and network traffic analysis to identify security weaknesses.
What is penetration testing in ethical hacking?
Penetration testing, or pen-testing, simulates cyber attacks on a computer system, network, or web application to identify vulnerabilities that could be exploited by malicious hackers.
Success stories
Can Great Learning Academy courses help your career? Our learners tell us how.And thousands more such success stories..
Related Cyber Security Courses
Popular Upskilling Programs
Explore new and trending free online courses
Relevant Career Paths >
What is Ethical Hacking?
Ethical hacking, also known as "white hat" hacking, refers to the practice of using hacking techniques to identify vulnerabilities and weaknesses in computer systems, networks, or applications. Unlike "black hat" hackers who engage in hacking for malicious purposes, ethical hackers are hired or authorized to find and fix security flaws to protect the confidentiality, integrity, and availability of information and data.
The goal of ethical hacking is not to cause harm, but rather to help organizations to identify and remediate security weaknesses before they can be exploited by malicious actors. Ethical hackers use the same tools and techniques as their criminal counterparts, but with the permission and oversight of the organization that they are testing.
Ethical hackers may work independently or as part of a larger security team, and they often perform a variety of tests, including network and application penetration testing, vulnerability assessments, and social engineering attacks. They may also use specialized software tools and manual techniques to identify and exploit weaknesses in a variety of systems and applications.
To be an effective ethical hacker, it is important to have a strong technical background in networking, programming, and security. Additionally, ethical hackers must be able to think creatively and strategically to identify potential attack vectors and ways to exploit vulnerabilities. They must also have a strong understanding of ethical principles and legal regulations in order to ensure that their testing does not cross any ethical or legal boundaries.
Overall, ethical hacking plays a critical role in ensuring the security and privacy of sensitive information in today's digital world. By proactively identifying and fixing vulnerabilities, ethical hackers help to prevent data breaches, cyber-attacks, and other security incidents that can have devastating consequences for individuals and organizations alike.
Here are some use cases of ethical hacking:
- Penetration testing: Ethical hackers are often hired by companies to test their networks and systems for vulnerabilities. This helps identify weaknesses that can be exploited by malicious hackers and provides an opportunity for the organization to address them.
- Security consulting: Ethical hackers can also provide consulting services to companies to help them improve their security posture. This includes identifying potential threats and providing recommendations for mitigating them.
- Incident response: Ethical hackers can assist in the aftermath of a security breach by identifying the source of the attack and providing recommendations for improving security to prevent future attacks.
- Security research: Ethical hackers often participate in security research projects to discover new vulnerabilities and develop new techniques for improving security.
- Cybersecurity education: Ethical hacking courses can be used to teach individuals about cybersecurity and help them develop the skills needed to protect their own systems and networks.
Reasons to learn ethical hacking:
- Job opportunities: Ethical hacking is a growing field with a high demand for skilled professionals. Learning ethical hacking can open up many job opportunities in the cybersecurity industry.
- Improved cybersecurity: By learning about ethical hacking, individuals can improve their own cybersecurity practices and protect themselves from malicious hackers.
- Professional development: Learning ethical hacking can be a valuable skill for IT professionals looking to advance their careers and increase their earning potential.
- Ethical hacking is legal: Unlike malicious hacking, ethical hacking is legal and can be used for the benefit of organizations and individuals.
- Personal interest: For some, learning about ethical hacking can be a fascinating hobby or area of interest. It can be a fun and rewarding way to explore the world of cybersecurity.
Why Ethical Hacking is in Boom?
With cyber threats on the rise, the demand for ethical hackers is skyrocketing. Ethical hackers are the frontline defenders of the digital realm, ensuring the security and integrity of systems. The boom in ethical hacking is driven by the need to stay ahead of cybercriminals and safeguard sensitive information.
Advantages of Taking This Course By enrolling in our "Introduction to Ethical Hacking" course, you gain a competitive edge in the world of cybersecurity. Here are some key advantages:
-
In-Demand Skills: Acquire the skills necessary to become a certified ethical hacker, a highly sought-after profession with lucrative career opportunities.
-
Protect Your Organization: Learn how to identify vulnerabilities in systems, networks, and applications, and secure them against malicious attacks.
-
Ethical Perspective: Understand the importance of ethical hacking, ensuring you use your skills responsibly and legally to make the digital world safer.
-
Career Growth: Ethical hacking is a dynamic field with continuous learning and growth opportunities. This course is your stepping stone to a rewarding cybersecurity career.
Check out our other programs
-
Free Course: Begin your journey with our free cybersecurity courses
-
Paid Course: Ready to take your skills to the next level? Deep dive into cybersecurity course







































.jpg)